Having also noticed flatware disappearances in academia…
Author: abigaildiscovers
Librarians on Reddit

WordPress for Libraries: , edited by Haefele, Chad

The US government is removing scientific data from the Internet | Ars Technica
At Ars Technica Live, we talked to Lindsey Dillon, who decided to do something about it.
Source: The US government is removing scientific data from the Internet | Ars Technica
earth :: a global map of wind, weather, and ocean conditions
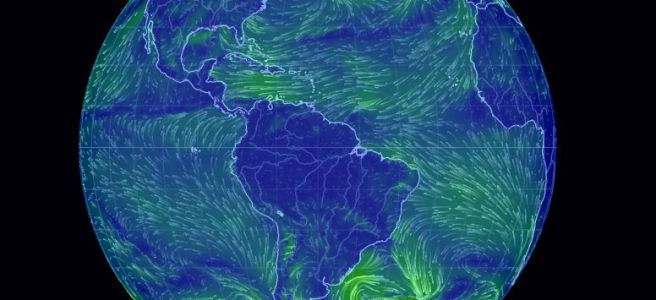
 See current wind, weather, ocean, and pollution conditions, as forecast by supercomputers, on an interactive animated map. Updated every three hours.
See current wind, weather, ocean, and pollution conditions, as forecast by supercomputers, on an interactive animated map. Updated every three hours.
Source: earth :: a global map of wind, weather, and ocean conditions
Digital Archaeology Project to Use Big Data

“This is not just a database,” said Ram, professor of management information systems and director of the INSITE: Center for Business Intelligence and Analytics in the UA’s Eller College of Management. “We’re building a knowledge discovery system that integrates multiple archaeological databases and various artifacts and objects, and we’re trying to figure out relationships that aren’t already known. People can query the website and it’ll show them various data and how they’re related to each other, and they’ll be able to run large-scale network analysis and statistical analysis that will support various stakeholders, including researchers and students, as well as the public.”
National Library Legislative Day 2017 Livestream – YouTube

OSF | Mission Possible: the Making of a Shared Digital Library


Hosted on the Open Science Framework – here is our presentation from the 2016 Digital Library Federation conference in Milwaukee.
Source: OSF | Mission Possible: the Making of a Shared Digital Library
Discovering Best Of Mass French Fries Results: Ranking the state’s best fries | masslive.com

After traveling across Massachusetts, the Best Of Mass. judges reveal the Top 10 french fry rankings.
Source: Best Of Mass French Fries Results: Ranking the state’s best fries | masslive.com
House library champions release FY18 “Dear Appropriator” letters
ALA asks advocates to ask their Representatives to sign two “Dear Appropriator” letters: one urging full funding for LSTA and the second for IAL program.
You can help!
Source: House library champions release FY18 “Dear Appropriator” letters – District Dispatch


